Vendor-agnostic
Choices follow outcomes, risk and operations context, not brand preference.
Design, orchestration and implementation guidance for existing and new environments.
Choices follow outcomes, risk and operations context, not brand preference.
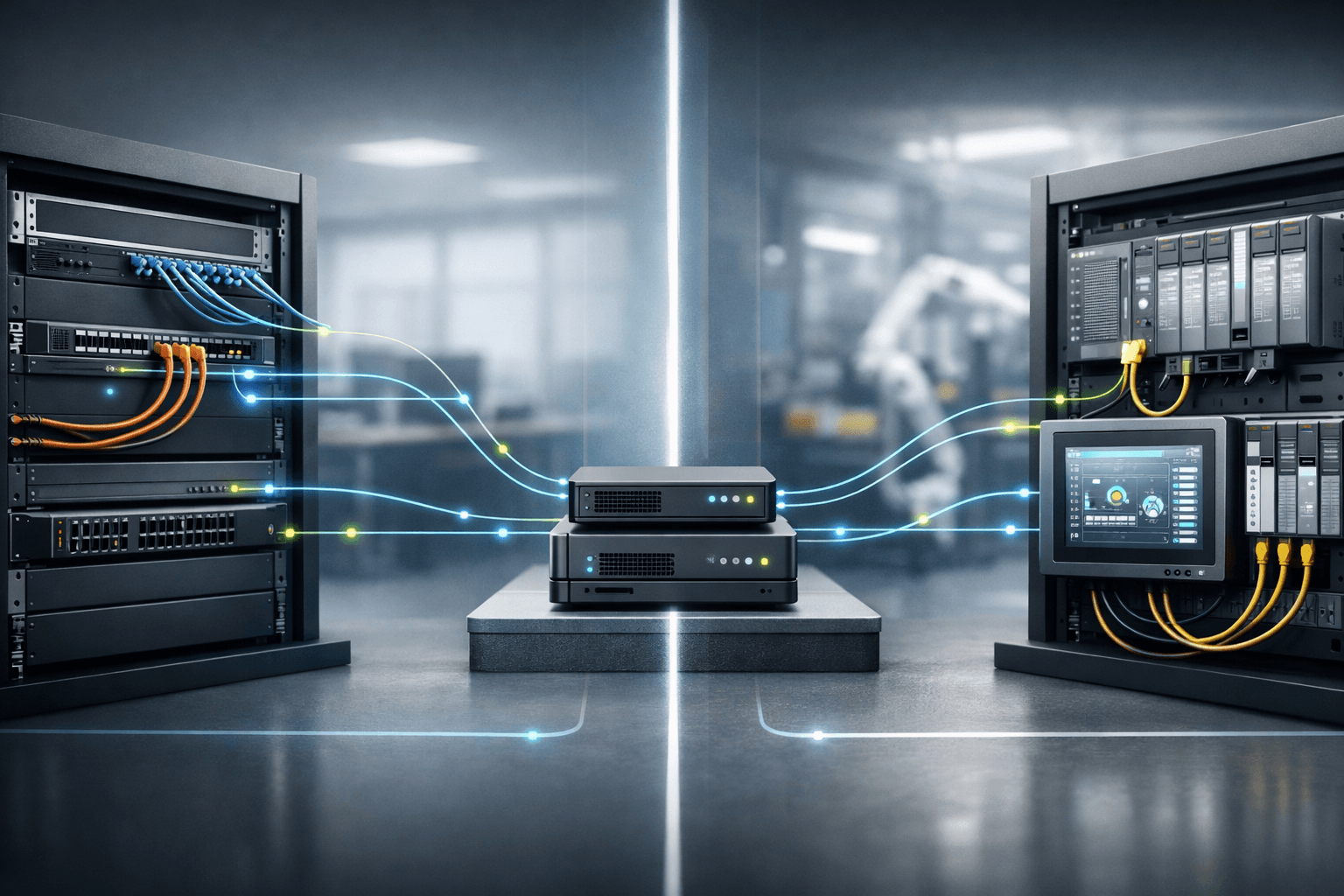
API integrations to IT systems and OT protocols such as Modbus, OPC UA and MQTT.
Services
Reliable integrations between OT, IoT/edge and IT with clear boundaries and ownership.
Page: /diensten/it-iot-ot-koppelingen
Segmentation, access and logging set up for control and traceability.
Page: /diensten/cybersecurity
From design and decision-making to execution, validation and handover.
Page: /diensten/regie-implementatie
Approach
Field experience
We bring engineering experience from heterogeneous environments, focused on integrations that remain stable in operations.
Security
Routes, access and logging are included from the start.
IEC 62443 is used as a reference model for structure and prioritization (not a compliance track).

Automation & AI
Developments move fast in IT, OT, IoT and the integrations between them. We apply this pragmatically with measurable value.
Tooling is a means, outcome and manageability remain leading.
No. We use IEC 62443 as a structure for prioritization and design decisions.
Only on request or with a partner. Primary focus is control design and implementation.
Yes. We start with baseline and risks, then improve in phases.
For IT/IoT/OT integrations, cybersecurity or implementation guidance.
Email · Phone · LinkedIn